|
|
||
|---|---|---|
| .circleci | ||
| .github | ||
| debian | ||
| docs | ||
| src | ||
| .gitignore | ||
| .gitmodules | ||
| .travis.yml | ||
| HAPPY_CUSTOMERS.md | ||
| LICENSE | ||
| README.md | ||
| THANKS.md | ||
Community Edition
FastNetMon - A high performance DoS/DDoS load analyzer built on top of multiple packet capture engines (NetFlow, IPFIX, sFlow, AF_PACKET, Netmap, PCAP).
What do we do?
We detect hosts in the deployed network sending or receiving large volumes of traffic, packets/bytes/flows, per second and perform a configurable action to handle that event. These configurable actions include notifying you, switching off the server, or blackholing the client.
Flow is one or more ICMP, UDP, or TCP packets which can be identified via their unique src IP, dst IP, src port, dst port, and protocol fields.
Integration with flow systems
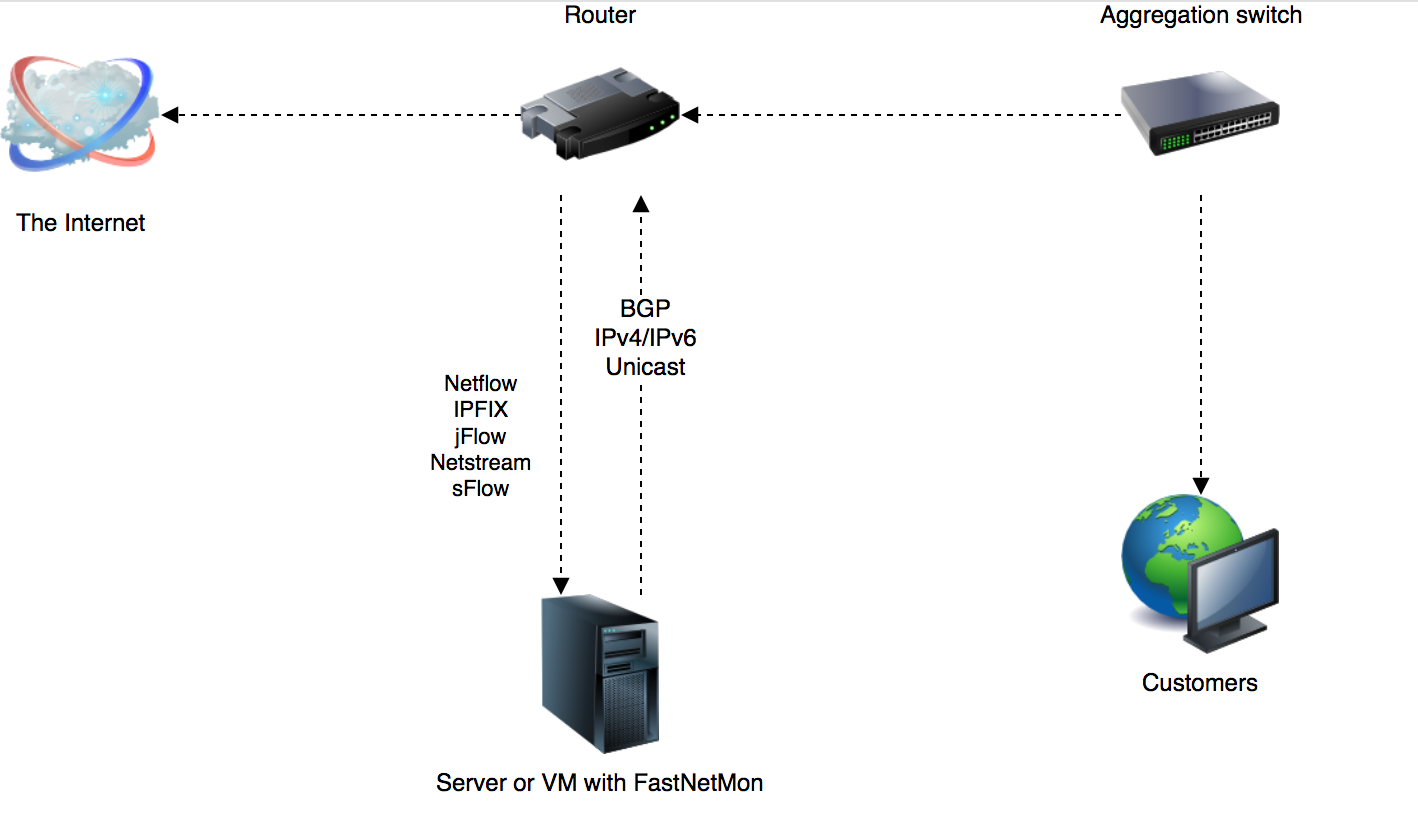
At a very high level integration with FastNetMon is fairly simple. In both cases the work flow is the same and the main difference being the port numbers provided. The port numbers are configurable.
sFlow
Configure the IP of the server running FastNetMon using port 6343. This port number is configurable.
Netflow
Configure the IP of the server running FastNetMon using port 2055. This port number is configurable.
License: GPLv2
Official mirror at GitLab
Project
- Official site
- FastNetMon Advanced, Commercial Edition
- FastNetMon Advanced and Community difference table
- Detailed reference in Russian: link
Official support groups:
- Mailing list
- Slack
- IRC: #fastnetmon at irc.freenode.net web client
- Telegram: fastnetmon
Follow us at social media:
Supported packet capture engines
- NetFlow v5, v9
- IPFIX
 v4, v5
v4, v5- PCAP
- AF_PACKET
- Netmap
- SnabbSwitch (experimental)
- PF_RING / PF_RING ZC (obsoleted, not recommented, please use AF_PACKET instead)
You can check out the comparison table for all available packet capture engines.
Complete integration with the following vendors
- Juniper integration
- A10 Networks Thunder TPS Appliance integration
- MikroTik RouterOS Please use only recent versions of RouterOS!
Features
- Detects DoS/DDoS in as little as 1-2 seconds
- Scales up to terabits on single server (sFlow, Netflow, IPFIX) or to 40G + in mirror mode
- Trigger block/notify script if an IP exceeds defined thresholds for packets/bytes/flows per second
- Complete support for most popular attack types
- Thresholds can be configured per-subnet basis with the hostgroups feature
- Announce blocked IPs via BGP to routers with ExaBGP or GoBGP
- Full integration with Graphite and InfluxDB
- API (available in master branch only)
- Redis integration
- MongoDB integration
- Netmap support (wire speed processing; only Intel hardware NICs or any hypervisor VM type)
- Filter NetFlow v5 flows or sFlow packets with LUA scripts (useful for excluding particular ports)
- Supports L2TP decapsulation, VLAN untagging in mirror mode
- Complete plug-in support
- Capture attack fingerprints in PCAP format
- Experimental BGP Flow Spec support, RFC 5575
Running Fastnetmon
Supported platforms
- Linux (Debian, CentOS, Ubuntu), x86_64 only
- FreeBSD: official port.
Hardware requirements
- At least 1 GB of RAM
Router integration instructions
Distributions supported
- Automatic install script for Debian/Ubuntu/CentOS
- We are part of the official FreeBSD ports collection
- Docker image
Screenshots
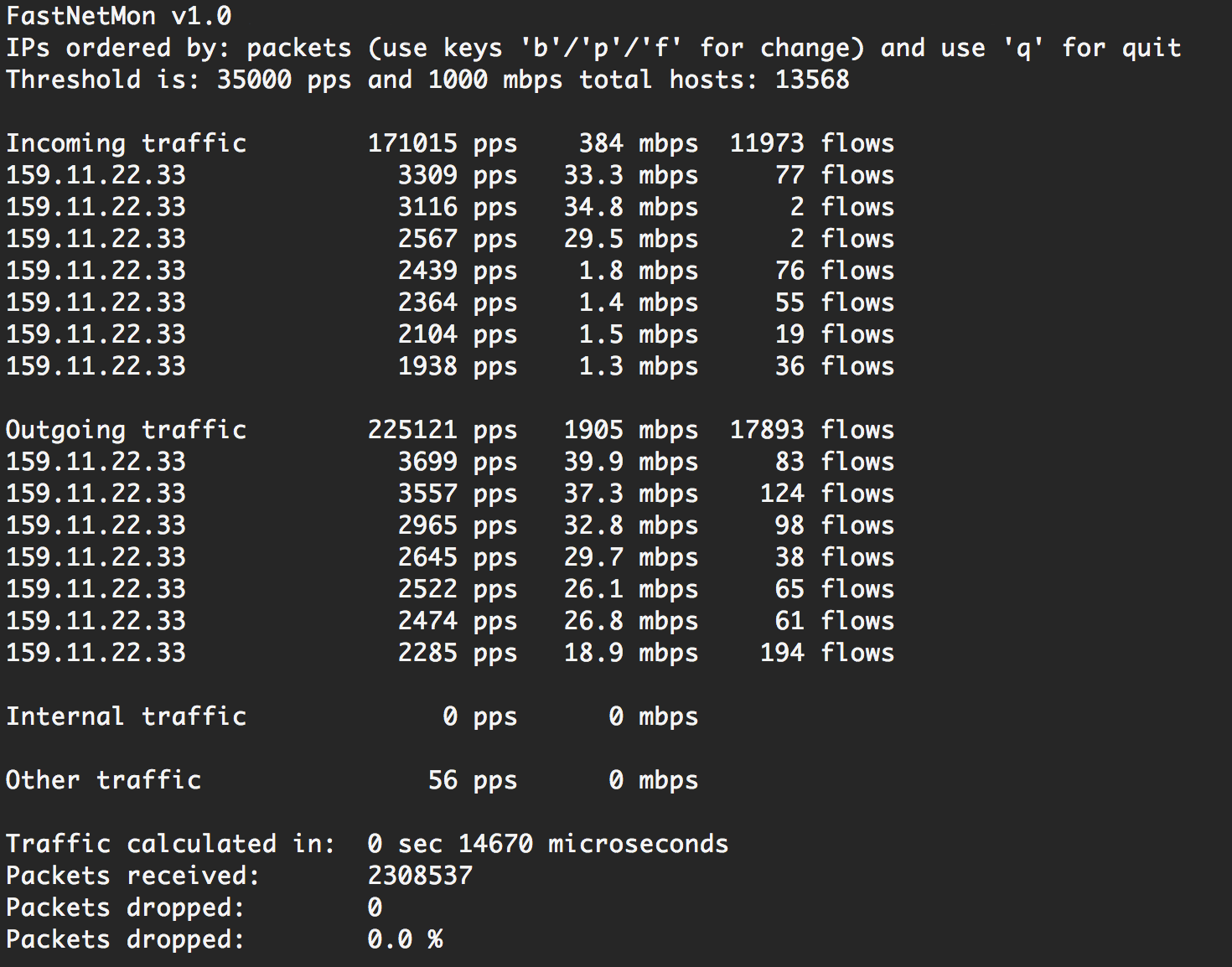
Main program:
Example CPU load on Intel i7-2600 with Intel X540/82599 NIC at 400Kpps load:

Example of notification email about detected attack:
Author: Pavel Odintsov